Aw, Snap! (or How I got Hacked)
So there I am surfing the web and catching up on some blogs and news when I notice my Skype icon blinking away at me in the windows taskbar. Hmm, someone’s sent me an IM, thinks I only to discover that Skype logged me out.
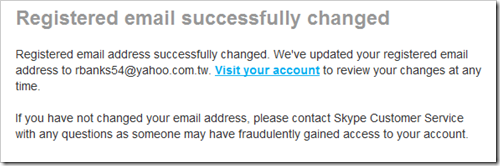
That’s weird I say to myself. I guess I’ll just log in again. Click. What? Invalid login? Hmm. Try again. Click! Click!! Click!!! Dammit! What’s going on. Oh look – I just got an email. It’s from Skype.
Aw, Snap!!! (or insert expletive of your choice).
Yes, my Skype account had been hacked and on gaining entry the attackers had immediately changed the account password and email address on me, blocking me out.
Long story short, the good news is that after immediately contacting Skype they restored my account to me (thank you!!) in less than 2.5 hours and it only cost me a few euro in Skype credits and a few hours of panic. Yet the whole thing was entirely preventable.
But How?
So the obvious question: how did it happen? Simple – I was stupid and lazy and forgot some of the basics of online security. Doh!
You see, when I’d first used Skype years and years ago, it was way back in it’s early days and at that time I used an insecure password. It was a dictionary word of all things – I know! I know! You don’t have to tell me! But because I was just trying the thing out I figured that if it was useful then I’d go back and change my password later on. At the time I’d also clicked the auto-login option and let Skype sign itself in for me.
Unfortunately, because I never used it much early on I never went back and changed the password, and over time forgot what it was. Kind of like when we tell ourselves we’re going to write those unit tests once we get this code working. The reality is that we get distracted or do something else, forgetting to go back and clean up after ourselves. As the saying goes, the road to hell is paved with good intentions.
Of course, at any point I could’ve done the “I forgot my password” routine, but as Skype kept logging itself in, I just forgot about it and fixing the password drifted to the bottom of my “stuff I should really do to be a good human being but that I’ll likely never get around to doing because I’d rather be sleeping or eating or having s..” well, cough, ahem, you get the idea.
Using a real word for a password all those years ago and not taking the one measly minute needed to fix it is pretty lazy of me, huh? Yet so many people do it. And it could’ve turned out so much worse. Thankfully that password wasn’t used anywhere else, so I didn’t have to worry about the hackers using that to break into other accounts of mine.
Of course, what irks me most is that these days I use KeePass and I’ve even blogged about it in the past (though I now use DropBox instead of Mesh for syncing), and I’ve read plenty of tales in the past of accounts being hacked and how easy dictionary based attacks are to pull off. And yet here I am. A victim. Grrr. Dumb, Richard. Dumb!
So what are my lessons? What do I learn from my dumbicity?
1. NEVER. Not ever. Not even on my deathbed will I use a weak password for anything. Even if it’s a throw away account to register for some software trial that I’ll never use again. I have Keepass and it can generate passwords for me that are safe.
2. Never reuse passwords across sites. Once a password is compromised on one site it’s compromised everywhere.
3. Keep my OpenId accounts extra secure. If I lose an OpenId account I’d be really messed up, especially as these days the use of OpenId is increasing and more and more sites are accessed only via OpenId accounts.
4. Go and change all those other passwords I have just in case. I can’t think of how many other sites I’ve used over the years that I no longer visit and where I may have old passwords laying around. If one of those sites was compromised and I’ve reused that password elsewhere and not realised it, what else can the attackers get to?
So, enough beating myself up about this. I’ve learned my lesson. Hopefully you can learn from my mistake as well and avoid being a statistic like me.